The team behind the community-created reverse engineering project for Rabbitude Rabbit R1there is revealed finding a security issue with company code that made users’ sensitive data publicly available. In an update posted on the Rabbitude website, the team said it gained access to the Rabbit codebase on May 16 and found “several critical hard-coded API keys.” These buttons allow anyone to read every response the R1 AI device makes, including users’ personal information. They can also be used to brick R1 devices, change R1’s responses, and replace device audio.
The API keys they found authorize users to access ElevenLabs’ text-to-speech service, Azure’s speech-to-text system, Yelp (for review searches), and Google Maps (for location searches) on the R1 AI device. In a tweet, one of the members of Rabbitude he said that the company had been aware of the problem for the past month and had “done nothing to fix it”. After sending, they said Rabbit cancelled Elevenlabs’ API key, although the update does break R1 devices a bit.
In a statement to Engadget, Rabbit said it was only made aware of the “alleged data breach” on June 25. “Our security team immediately began investigating this,” the company said. “At this time, we are not aware of any breach of customer data or any compromise of our systems. If we learn of any other relevant information, we will provide an update once we have more information.” Rabbitude did not say whether its team had revoked the keys it said it found in the company’s code.
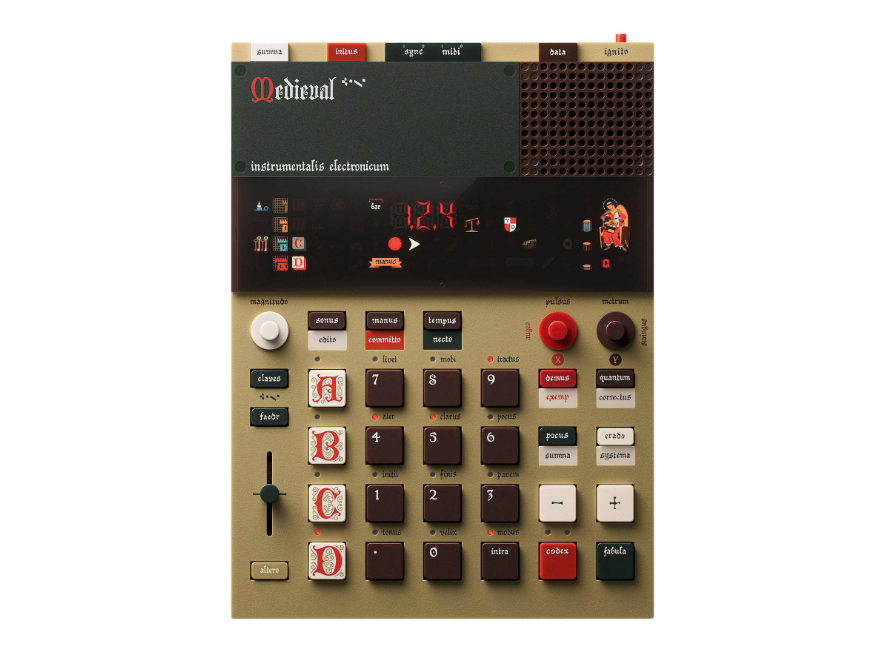
Rabbit’s R1 is a standalone AI assistant device developed by Teenage Engineering. It is designed to help users perform certain tasks, such as placing food delivery orders, as well as quickly look up information such as the weather. We gave a fairly low score overview, because we found that its AI functionality often didn’t work. In addition, users can simply use their phone instead of spending an additional $199 to purchase the device.